Blockchain is a hype topic that already led to some disillusionment. The development of blockchain-based applications is nowadays often technology-driven and with a trial-and-error approach. We provide foundational guidance for architecting blockchain-based applications. We put structure on key foundations and terms around blockchain, we outline architecture drivers that benefit from using blockchain technology, and we guide architects with numerous questions through the design space of blockchain-based applications.
①Needs | ①Foundations | ②Blockchain Terminology | ③Architecting Guidance | ③Get Started
This article is the first of a three-article series (①②③) on architecting blockchain-based applications. The series is based on results of an internal workshop of the Fraunhofer IESE department ACE (Architecture-Centric Engineering) in 2018.
Authors (main editors underlined): Susanne Braun, Frank Elberzhager, Matthias Gerbershagen, Andreas Giloj, Sebastian Heupts, Steffen Hupp, Alberto Lara, Rodrigo Falcão, Matthias Naab, Kai Plociennik, Bernd Rauch, Dominik Rost, Johannes C. Schneider, Stefan Schweitzer, Adeline Silva Schäfer, Balthasar Weitzel.
If you want to develop innovative ideas, architectures, and prototypes of applications based on blockchain technologies: Don’t hesitate to contact us!
The Need for Precise Terminology and Architecting Guidance
The rise of the Bitcoin currency made blockchain known to a vast majority of people in the IT business and even the overall population. We could get the impression that at least the finance world will undergo a major revolution in the next years because of blockchain technology, which both new and traditional companies are exploring. While the projected impacts and visions are immense, real applications beyond crypto currencies are not wide-spread, yet.
The development of blockchain-based applications is nowadays often technology-driven and done with a trial-and-error approach. The goal of most companies is to gather first experiences and to learn about technologies and potentials. Available literature is either extremely technical and detailed or high-level and visionary. Additionally, we found in literature that key terms are often confused and used in an overloaded way. Nevertheless, architects need to be able to reason precisely when architecting blockchain-based applications and make well-informed decisions on central architectural questions. This is especially important because the developed applications are used for handling data that is of high relevance to the users. Hence, we decided to give guidance for architecting blockchain-based applications in the following way:
- In this article, we describe key topics and terminology of blockchain technology and applications which we consider to be important when architecting blockchain-based applications.
- Key terms around blockchain are often confused and used in a not clearly delineated way. In the second article of our series, „What Do You Really Mean by ‚Blockchain‘?“, we provide a blockchain terminology that clearly delineates the central concepts we think one has to be able to precisely reason about when architecting such applications.
- When architecting blockchain-based applications, care has to be taken to make well-informed decisions on central architectural questions that impact the application’s properties. This is not an easy task due to the complex nature of the blockchain concept and its applications, and due to the importance of the handled data. In the third article of our series, „Guidance for Architecting Blockchain-Based Applications“, we give guidance to find out whether using blockchain technology is an adequate choice for the given application, and we guide architects to make well-informed and understood architecture decisions.
The following figure summarizes the contents of our article series.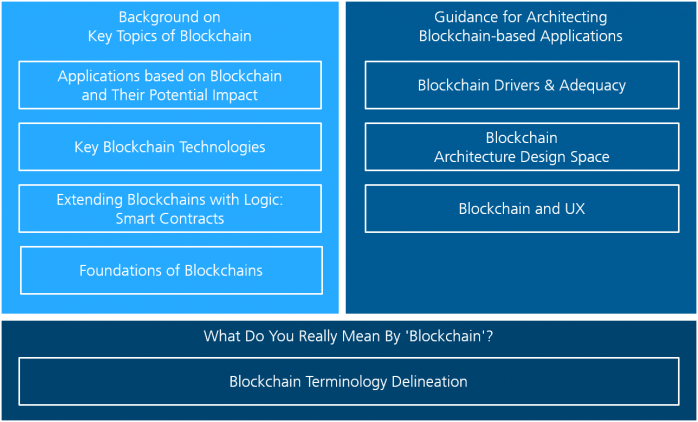
Background on Key Topics of Blockchain
Foundations | Smart Contracts | Technologies | Applications & Impact
Blockchain Foundations
The purpose of a blockchain is to be a public digital ledger that is operated by peer participants in a distributed way. The participants want to keep track of transactions that they make, and they want to make sure that the record of transactions cannot be tampered with, so that everyone can rely on unaltered data in the transaction record. This is achieved without the need for a central authority, since a blockchain is made up from peer nodes. Hence, blockchain technology enables the development of innovative applications that are easily scalable and robust, without the need for up-front invest in IT infrastructure. Since the concrete concept of „what a transaction is“ can be handled in a flexible way, this includes applications such as the well-known crypto-currencies Bitcoin and Ethereum, where the transactions refer to value in some currency system, but also other applications are conceivable such as ones where the transactions refer to files in a distributed file system or to commitments in a legal system.
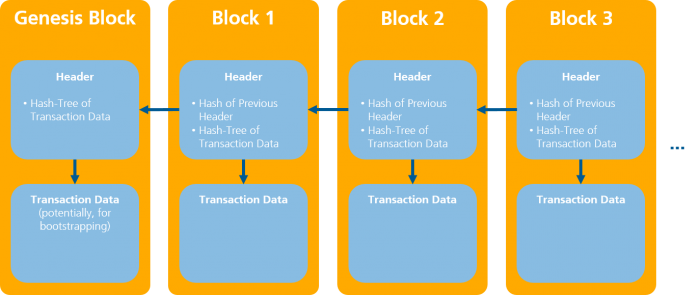
In the absence of a central authority, the system of peer nodes forming the blockchain determines the correct state of the ledger via a consensus algorithm. In the consensus algorithm, the nodes negotiate the correct state of the ledger by executing a certain communication protocol and „voting“ for the next state. The basic idea here is that the transaction data in the blockchain is stored in a sequence of data blocks, to which new blocks can be appended. In principle, any node in the system can append a new block of data to the sequence, which is called mining. The following figure gives an overview on how data is stored in the sequence of data blocks:
Starting with an initial genesis block containing potential bootstrapping information, blocks of transaction data are mined as described above, i.e., appended to the existing sequence of blocks. This is done using cryptographically safe, i.e., collision-resistant, hash functions to link blocks and data: The hash values computed for previous blocks‘ headers and the hash trees computed for the transaction data in a block certify the integrity of the referenced data, since by collision-resistance of the used hash functions, it is computationally hard to find different data (in a try to manipulate the blockchain) with the same hash value. Hence, one assumes that no such attempt will succeed and integrity of the blockchain will be given.
In a public, permissionless blockchain, where anybody can participate in the mining process, there is a risk that a node might be malicious. Hence, certain „proof concepts“ are used in different blockchain technologies: Nodes must prove to act in the interest of the whole community when mining blocks of new transaction data. A popular proof concept, used e.g. in the Bitcoin technology, is Proof of Work (PoW), where a node is required to solve some computationally hard problem before being able to append a new block of data to the chain. This makes it hard to alter the data in the blockchain in a malicious way, since one would need a very large amount of computational resources to succeed in manipulating the consensus process in which the nodes vote for the correct state of the ledger. However, e.g. in a so called 51 % attack, where a malicious party possesses 51 % of the computing resources in the system, an attack could be successful.
To summarize, the approach to provide a public digital ledger without a central authority is attractive, but one has to be aware that there is a price one has to pay for that:
- Firstly, unalterability of the data in the ledger is not guaranteed. This is due to the fact that as mentioned, it is computationally hard but not impossible in a strict sense to alter the data in the ledger in a malicious way, since e.g. a 51 % attack is possible, where a malicious party can take over control of the blockchain and harm other participants.
- In case the concrete blockchain uses proof of work as a proof concept, we can observe a second price one has to pay: Energy consumption can become very high if the system grows, as has happened e.g. for the Bitcoin network. Also, the fact that a consensus algorithm replaces the need for a central authority leads to the fact that using blockchain technology, transactions tend to be slower than in centralized systems, since more complicated computational tasks have to be executed to add data to the ledger than in a more simple, centralized system.
Whether one is willing to pay the price of not having a guarantee on unalterability of the data in the ledger is a question of the concrete application that has to be developed. With respect to the second point, we mention that depending on the concrete setting in which the blockchain should be used, problems such as the mentioned high energy consumption using proof of work can be attenuated:
- In a public, permissionless blockchain, where anyone can participate in the consensus process and nodes are actually peer, concepts such as proof of work are needed, since one does not know which nodes might be malicious. However, in a blockchain operated by a single company or a consortium of companies, i.e., a private or federated one, access to the blockchain could be restricted to a preselected set of nodes, and also the right to modify the data in the ledger and to mine nodes might only be given to certain nodes which have to authenticate to do so. No proof of work is needed here, alleviating the energy consumption problem. Also, an intermediate solution of a public but permissioned blockchain is possible.
- Also, other concepts than proof of work exist, each with its own advantages and disadvantages. For example, in Proof of Capacity (PoC), a node has to prove that it possesses a certain amount of storage capacity, thereby replacing the computing resources from proof of work by storage resources, with advantages in energy consumption.
- Another example is Proof of Stake (PoS), where a node has to prove to possess a certain share of the total value in the system to be able to participate in the mining process. Intuitively, the ability to influence the data in the ledger scales with the possessed share of total value in this concept. The goal here is analog to the one for proof of work: Make it unlikely that a malicious party can attack the blockchain, since the party would need to possess a large fraction of the total value in the system (for crypto-currencies: the total amount of monetary value). However, from the real world, we know that large fractions of the total amount of private assets can well be concentrated in the possession of a minority of participants, making an attack potentially possible.
Smart Contracts
“A smart contract is a computer protocol intended to digitally facilitate, verify, or enforce the negotiation or performance of a contract. Smart contracts allow the performance of credible transactions without third parties by using trackable and irreversible transactions.” This definition outlines all aspects that are crucial to smart contracts. In the context of blockchains, when we talk about a smart contract, we usually mean program code being executed on the runtime environment provided by the blockchain.
In contrast to traditional contracts, no authorized third parties as e.g. notaries, the government, or a centrally trusted bank are needed to guarantee the fulfillment of a contract. Instead, contracts are enforceable by their program code, which is expressed by the so-called “code as law” principle.
The fact that smart contracts are stored on the blockchain in an unchangeable way has two crucial consequences:
- Every smart contract published on a blockchain is visible to everyone participating in the blockchain. This includes the bytecode and the internal state of a smart contract. In the case of public blockchains, this means that everybody with internet access can read every detail of every smart contract. Hence, it is not possible to store secrets inside the smart contract code.
- There is no possibility to rework or even revoke a smart contract once it has been published. Since we all know that programs can have bugs, this can lead to big problems, which is not a theoretical consideration: An undesired and unforeseen behavior in the contracts that define the Decentralized Autonomous Organization made it possible for a hacker to extract an equivalent of $70 million from the contract, which finally lead to a hard fork of the Ethereum blockchain.
The implementations of smart contracts differ depending on the blockchain technology. In Ethereum, one of the most popular platforms for smart contracts, smart contracts are usually written in a C-like programming language Solidity, which compiles to byte code that is finally stored on the blockchain. The effective computing capabilities of smart contracts are limited. There are two main reasons for this:
- Whenever an Ethereum node verifies a transaction that includes the execution of a smart contract, it runs the code in a sandboxed and isolated virtual machine. Since this has to be done by every verifying node, only limited computing resources are available.
- Every person that executes a method of a smart contract has to pay a price (expressed in the unit “gas”) that depends on the effective number of instructions and memory usage of this method call.
Thus, complex calculations easily become very expensive. To put it with the words from the Ethereum Development Tutorial: “Roughly, a good heuristic to use is that you will not be able to do anything on the EVM that you cannot do on a smartphone from 1999.”
While there are lots of simple use cases that one can build with a single smart contract, e.g. ledgers for own crypto currencies or tokens, more complex applications are usually built by combining several smart contracts together, which is possible since one smart contract can call functions from another smart contract. Because there is no single point to attack such decentralized applications (DApps), they are highly fault-tolerant and very difficult to attack. On the other hand, DApps are difficult to build (complex protocols, few ready-to-use components), difficult to maintain (bug fixing) and difficult to extend (updates, scaling). In Ethereum, operating a DApp can also become more expensive compared to regular apps due to a so-called gas fee which has to be payed to the mining node every time a function of a smart contract is executed.
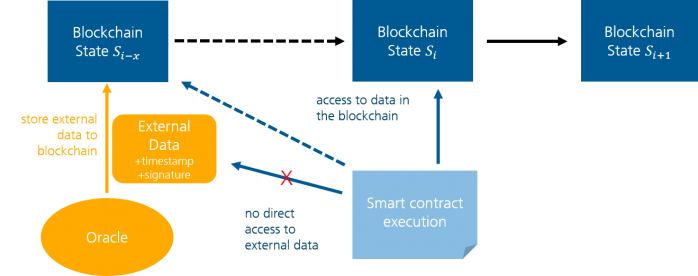
We have already mentioned that a smart contract can access data from the blockchain and from other smart contracts. However, many real world contracts concern external data like stock prices, weather data, flight (delay) schedules or sensor data of IoT devices. In the smart contract/blockchain context, so-called oracles provide this data by storing it in the blockchain. There are different approaches to oracles, the simplest being trusted third party service provider that add a timestamp to the data and digitally sign it, which, however, adds again dependency to single authorities. Other mechanisms include a consensus protocol of several independent trustees or a web of trust.
Use cases for smart contracts have been discussed a lot in the past. They reach from simple conditional payments (e.g. money back on flight delay) over decentralized government (voting and publishing of elections in the blockchain), economy of things, health data (with automatic health insurance handling) up to rental agreements (of apartments, bikes, cars in combination with smart locks) and (software) license management. However, few of these use cases are in fact implemented and established at the time of writing this article. Ethereum has a list of available DApps, where you can find applications mostly from the sectors gaming/gambling and financial trading/exchanges, the first belonging to “let’s try out what is possible with this new technology” and the latter being the most typical blockchain use case: speculation with crypto coins.
Blockchain Technologies
Many different blockchain technologies are available today. Unless some very special use case has to be handled and someone with expert knowledge in cryptography and network protocols is available, we recommend choosing from already existing technologies.
We give a brief description of 5 well-known technologies:
- Bitcoin Core is the original and reference implementation for the Bitcoin cryptocurrency. It is licensed under MIT license and is maintained by an open community where the release process is managed by a team of developers. The Bitcoin network is permissionless, employs Proof of Work as consensus algorithm and it has a cross-industry focus, targeting no concrete use case. Bitcoin Core supports Smart Contract functionality through extensions with scripts. There is a second implementation of Bitcoin, Bitcoin Cash, which is a fork of Core created in 2017.
- Ethereum is a blockchain technology maintained by the Ethereum Foundation and Ethereum Alliance. Ethereum is licensed under different models depending on the component. It is permissionless and employs proof of work as consensus algorithm, although the goal is to move to a proof of stake algorithm. It has a cross-industry focus, originating from the banking and finance sectors. Ethereum supports smart contract functionality and provides the cryptocurrency Ether.
- Hyperledger is a set of open source tools and frameworks for blockchains, which is developed under the leadership of the Linux foundation. Many big tech companies, like Airbus, IBM and Intel, support its development. The best-known framework originating from this project is Hyperledger Fabric. Its architecture allows the flexible combination of the different building blocks of a blockchain in a plug-and-play manner. With the different frameworks and tools of the Hyperledger project you can create permissioned and permissionless blockchains with different consensus algorithms.
- Monax, previously Eris, is a blockchain technology based on Ethereum and owned by Monax Industries Limited. It is licensed under GPLv3. Monax network is permissioned and employs a Byzantine fault-tolerant Tendermint consensus engine, which is a deposit based proof of stake protocol. It has a cross-industry focus and it was designed as an easy to use blockchain technology that can be integrated rapidly by companies. Monax was designed to support Smart Contracts.
- Ripple is no blockchain technology, but a distributed open source protocol for a currency exchange network. The creators of ripple publish the source code under the ISC license. Under the hood, it uses a XRP Ledger. It is permissioned and the basis for its consent algorithm is a divide-and-conquer approach, which divides large networks into collectively trusted subnetworks.
Blockchain-Based Applications and Their Potential Impact
Dragged by the successful use case of Bitcoin, numerous initiatives have been started to, somehow, surf on the “blockchain wave” – which has led to a multitude of applications that are so exotic to the point that some people, not without a reason, consider Blockchain “a solution searching for a problem”. Examples include the end of poverty and human suffering, the cure of cancer, the ownership shares of ancient sunken treasures, among many, many others.
Hype and Frustration
The hype around blockchain finds particular expression in numerous articles and statements about the potential impact of blockchain and the expectations towards it:
- Blockchain Technology is the Most Significant Invention since the Internet and Electricity
- Blockchain: The Invisible Technology That’s Changing the World
- How blockchains could change the world
- What is blockchain? The most disruptive tech in decades
- Beyond bitcoin: How cryptocurrency is changing the world
- Eight Ways Blockchain Will Impact The World Beyond Cryptocurrency
- 3 Biggest Ways Blockchain Will Change Society
- How blockchain is changing money and business
At the same time, there are also counterarguments and criticism of blockchain or the way how the world looks at it. To be really heard, they formulate their statements strongly, too:
- Ten years in, nobody has come up with a use for blockchain
- There’s No Good Reason to Trust Blockchain Technology
- Blockchain is not only crappy technology but a bad vision for the future
“There is no single person in existence who had a problem they wanted to solve, discovered that an available blockchain solution was the best way to solve it, and therefore became a blockchain enthusiast.”
Central Characteristics of Blockchain for Applications
The following key characteristics come with the usage of blockchain technologies and can be employed to come up with beneficial and innovative applications.
- Decentralization
- Peer-to-peer communication
- Data immutability
- Transparency
- Automated contract logic
In recent years, initial scientific works such as “Do you need a blockchain” have been published aiming at providing support on how to properly identify use cases for blockchain, and figuring out in which type of blockchain a potential application would fit.
Potential Impacts and Benefits of Blockchain
Independent of concrete application domains, impacts and patterns of blockchain can be identified. The following impacts (which mostly express particular quality properties of the resulting applications) can be found in recent applications and in literature:
- Removal of intermediaries and decentralization
Many established businesses rely on central authorities and expensive intermediaries and middlemen, which are perceived to dictate and add costs and to delay the business. The idea is the get rid of the intermediaries and come up with direct business relationships among parties.
However, it is often neglected that the intermediaries might add much more services and benefits than just the pure transaction. Additionally, the trust moves from authorities to software and algorithms. - Transparency and rebalancing of information symmetry
Established businesses are often perceived as not transparent and giving certain parties an informational disadvantage. This should be overcome by more transparency of information placed in blockchains. - Resiliency against attacks, proof of authenticity, and preventing fraud
In traditional businesses and information systems, there is often a central authority, which can be attacked for various reasons. The distributed character of blockchains is expected to make certain attacks and fraud extremely hard or even impossible. The authenticity of data can be proven without trusting a third party. This might be in particular interesting in contexts where trustworthy central authorities are rare (e.g. in areas with unstable governments).
However, the overall trust and authenticity still relies on the trustworthiness of people entering data and a trustworthy access to the blockchain-based application itself (there might be intermediaries, which bundle the access of users to the blockchain). - Operational efficiency and removing human variance
While many traditional business processes still heavily rely on human work and intervention, in particular when it is about contracts and legally binding transactions, blockchain and in particular smart contracts promise to strongly increase the degree of automation. Additionally, distributed and heterogeneous data silos should be broken up and consolidated in central blockchain storages.
However, the operational efficiency is often traded off against a strongly increased energy consumption.
Example Blockchain-Based Applications
Existing blockchain applications are spread across diverse domains. Examples include:
- Everledger provides a global digital ledger that tracks and protects valuable assets throughout their lifetime journey. E.g. 1.6 million diamonds are tracked on the blockchain including central data attributes like color, carat and a certificate number, which can be also inscribed on the stone. Thus, the blockchain data becomes the digital twin of the diamond. The data is entered by manufacturers and retailers of diamonds.
- In the financial market, the Australian’s biggest stock exchange, ASX, has decided to adopt blockchain in order to improve the efficiency in post-trade processing, cutting the costs of transactions, and making them faster and more secure. They expect that the “new system will be able to save as much as $23 billion once implemented”;
- In the energy domain, Brooklyn Microgrid is developing a community-powered microgrid in Brooklyn, NYC – an automatic logging on the blockchain quickly shows who has produced or consumed how much electricity in the last billing period, and because the data is stored decentrally, the producers are independent of the energy companies and can still be sure that no one cheats the other.
- In the public sector, the government of Estonia has launched an E-Residence program that allows any person in the world to have a digital ID that offers the opportunity to start and manage an EU-based business from anywhere on the earth. The health care system in Estonia runs also on a blockchain to ensure data security.
- In the public sector, FollowMyVote offers a secure online voting platform providing greater election transparency. Voters can verify that their vote was not tampered with. The voters remain private while the overall results are transparent for everyone.
- In Switzerland, citizens have a blockchain-based e-ID, and their elections are based on these IDs.
- In the real estate market, Vermont city (in the US) launched a pilot program to use blockchain to record property transactions, to reduce costs related to paper process and human verification.
Legal Issues
This article has no focus on legal issues of blockchain. However, this is a very important topic in the overall design and operation of blockchain-based applications. Looking at the potential impacts and benefits outlined above, it becomes directly clear, that blockchain needs very thorough legal consideration as it often touches very sensitive data and it typically spans the boundaries of organizations. Some aspects to be considered are:
- The law of which country applies if there are transactions across country borders?
- What is the relationship to GDPR and which data can be made transparent, which data needs the possibility to be deleted later on?
- What is the relationship between a smart contract and a real-world contract?
For some further introduction to this topic, we recommend an article about key legal issues of blockchain by Osborne Clarke.
Continue with the second article of our series: „What Do You Really Mean by “Blockchain”?“